| |
| Main Page |
| Blog |
| Search |
| FAQ |
| TOP 10 |
| Pad Files |
| Contact |
| About... |
| Donate |
| All Utilities |
| Password Tools |
| System Tools |
| Browser Tools |
| Programmer Tools |
| Network Tools |
| Outlook/Office |
| 64-bit Download |
| Panel |
| Forensics |
| Pre-Release Tools |
| Articles |
Related Utilities
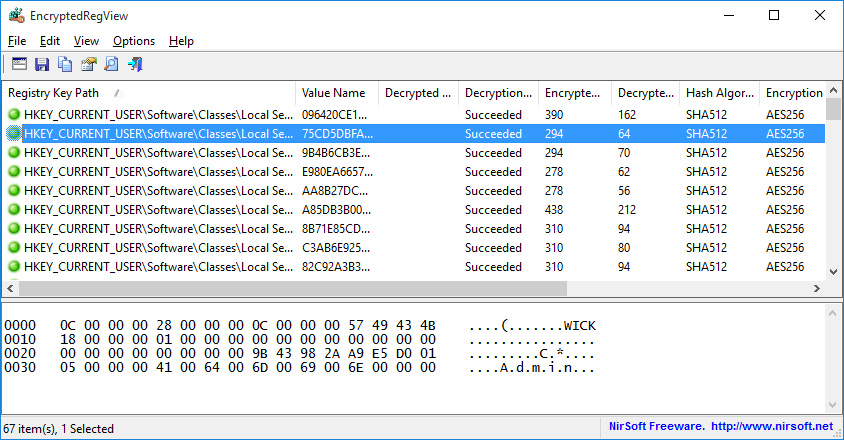
DescriptionEncryptedRegView is a tool for Windows that scans the Registry of your current running system or the Registry of external hard drive you choose and searches for data encrypted with DPAPI (Data Protection API). When it finds encrypted data in the Registry, it tries to decrypt it and displays the decrypted data in the main window of EncryptedRegView. With this tool, you may find passwords and other secret data stored in the Registry by Microsoft products as well as by 3-party products.
System RequirementsThis utility works on any version of Windows, starting from Windows XP and up to Windows 11. Both 32-bit and 64-bit systems are supported.
Versions History
Start Using EncryptedRegViewEncryptedRegView doesn't require any installation process or additional DLL files. In order to start using it, simply run the executable file - EncryptedRegView.exeAfter running it, the 'Advanced Options' window is opened and allows you to choose the settings of the Registry scan. By default, EncryptedRegView offers you to scan the Registry of your current running system and current user, without elevation (Run As Administrator). If you check the 'Run as administrator to decrypt system protected data' option, EncryptedRegView will be executed as Administrator (elevation) and then it might be able to decrypt system protected data that cannot be decrypted with normal user privilege.
After pressing the 'OK' button, EncryptedRegView starts to scan the Registry and searches for DPAPI-encrypted data.
When it finds encrypted data, it tries to decrypt it. If EncryptedRegView successfully decrypts the data, a new item is added to the upper pane with
'Succeeded' in the 'Decryption Result' column and green icon.
You can look at the entire decrypted information as Hex-Dump format in the lower pane by selecting the desired item in the upper pane.
If the decrypted information is a string, it's also displayed in the upper pane under the 'Decrypted Value' column.
Scanning Registry In External Hard DriveEncryptedRegView also allows you to scan the Registry of external hard drive plugged to your computer. In order to easily scan the Registry in external hard drive, choose the 'Scan the Registry of external drive' option in the top combo-box and then choose or type the path of the external drive and click the 'Automatic Fill' button. EncryptedRegView automatically fills for you the correct folders on the external drive (Registry Hives Folder, User registry file, User classes registry file, Protect Folders). Be aware that EncryptedRegView chooses the user profile (c:\users\[Profile Name]) with the latest modified time, so you may need to manually replace the paths if you want to scan another user profile.Also, in order to decrypt user-encrypted data on external drive (usually stored under HKEY_CURRENT_USER key), you must provide the correct logon password of the user. In order to decrypt system-encrypted data on external drive (usually stored under HKEY_LOCAL_MACHINE key), there is no need for the logon password in order to decrypt the data.
Failure ReasonsEncryptedRegView may fail to decrypt DPAPI data due to one of the following reasons:
Columns Description
Translating EncryptedRegView to other languagesIn order to translate EncryptedRegView to other language, follow the instructions below:
LicenseThis utility is released as freeware. You are allowed to freely distribute this utility via floppy disk, CD-ROM, Internet, or in any other way, as long as you don't charge anything for this and you don't sell it or distribute it as a part of commercial product. If you distribute this utility, you must include all files in the distribution package, without any modification !
DisclaimerThe software is provided "AS IS" without any warranty, either expressed or implied, including, but not limited to, the implied warranties of merchantability and fitness for a particular purpose. The author will not be liable for any special, incidental, consequential or indirect damages due to loss of data or any other reason.
FeedbackIf you have any problem, suggestion, comment, or you found a bug in my utility, you can send a message to nirsofer@yahoo.com
EncryptedRegView is also available in other languages. In order to change the language of EncryptedRegView, download the appropriate language zip file, extract the 'encryptedregview_lng.ini', and put it in the same folder that you Installed EncryptedRegView utility.
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||